adrik123adi
Well-known member
QZK RAT 2026
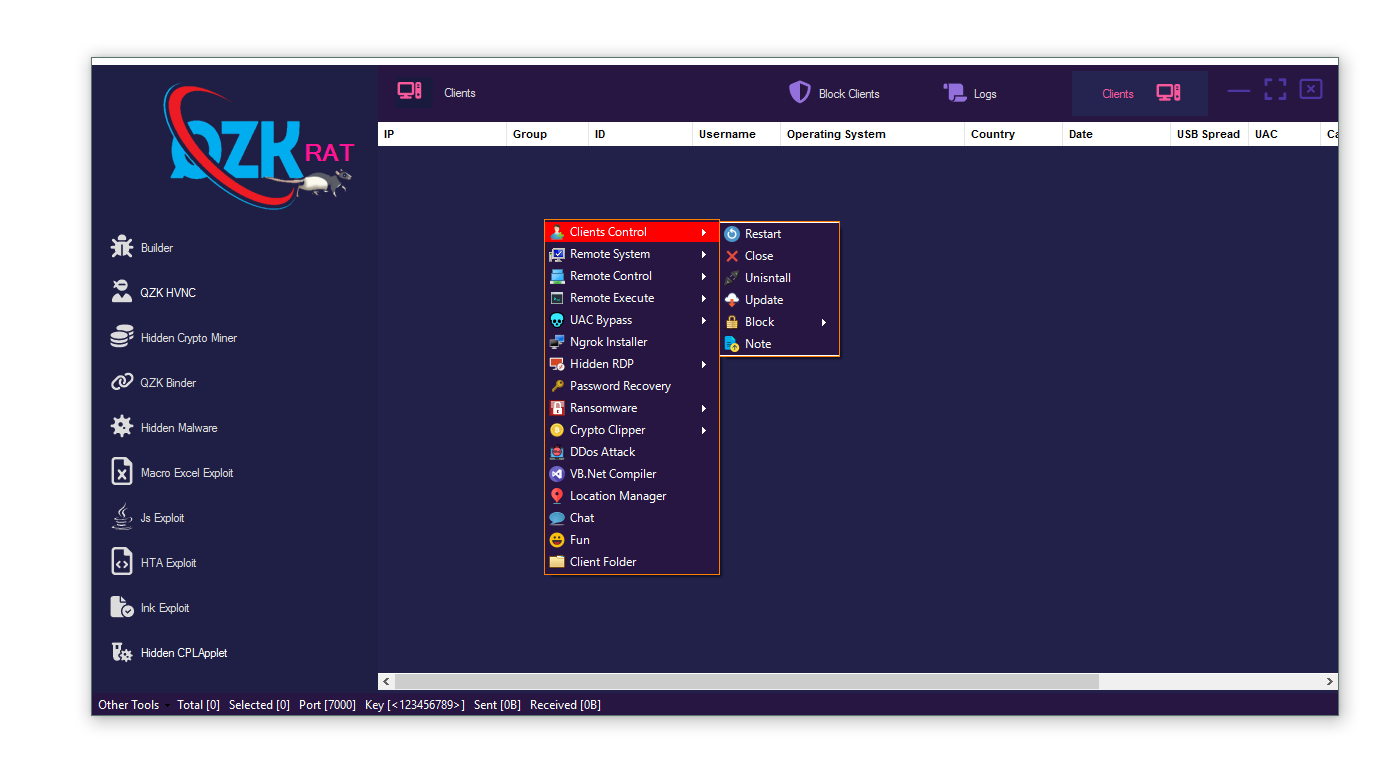
QZK RAT 2026 is a next-generation modular Remote Access Trojan (RAT) designed for cybercrime operations including remote surveillance, ransomware deployment, cryptocurrency theft, hidden mining, and credential harvesting. Unlike traditional malware, QZK RAT 2026 combines multiple attack modules into a single management dashboard, allowing attackers to control infected systems remotely while remaining highly stealthy. Security researchers consider it a dangerous multi-functional malware framework due to its advanced persistence, evasion, and monetization capabilities.
QZK RAT 2026 Feature List
Remote Access Control: Full remote system monitoring and administration capabilities.
Password Recovery: Steals saved browser credentials and authentication data.
Remote Desktop Monitoring: Allows attackers to view and control victim desktops remotely.
Microphone Access: Enables hidden audio recording from infected devices.
Webcam Surveillance: Provides unauthorized access to victim webcams.
Keylogger: Captures keystrokes including passwords and sensitive communications.
Crypto Clipper: Replaces copied cryptocurrency wallet addresses for financial theft.
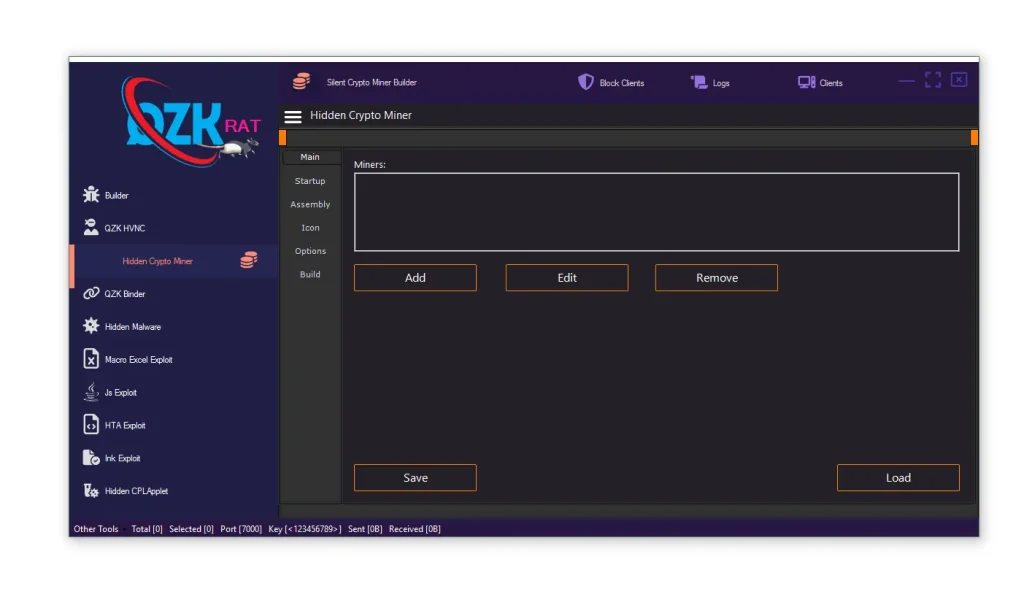
Hidden Crypto Miner: Uses victim hardware resources for silent cryptocurrency mining.
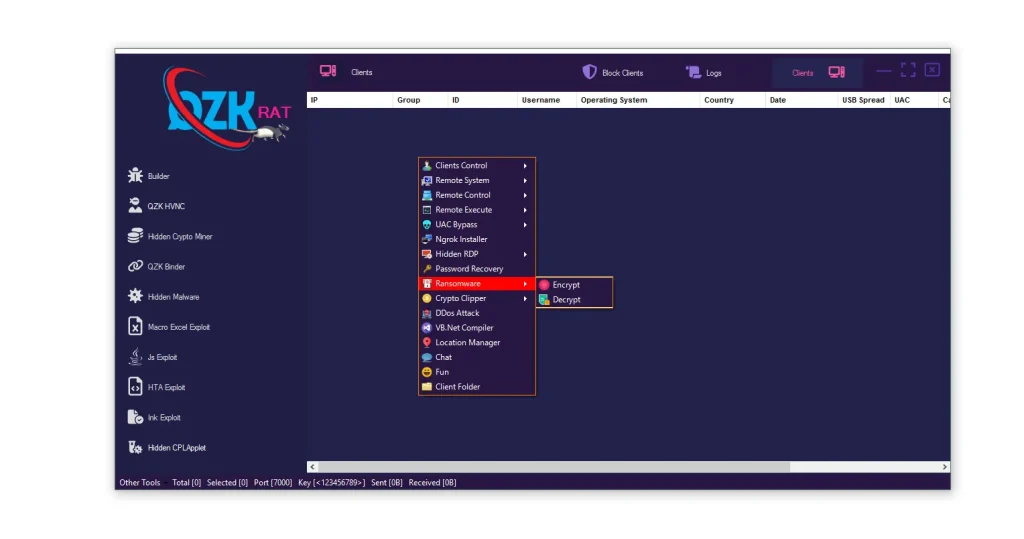
Ransomware Module: Encrypts files and supports extortion-based attacks.
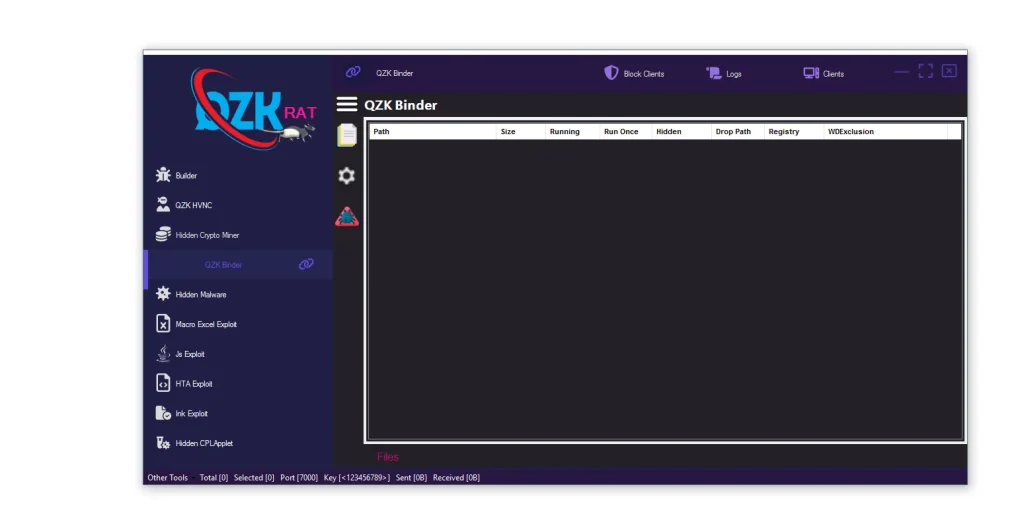
QZK Binder: Combines malware with legitimate-looking files for stealth delivery.
HTA Exploit Builder: Creates malicious HTA payloads capable of executing scripts on Windows.
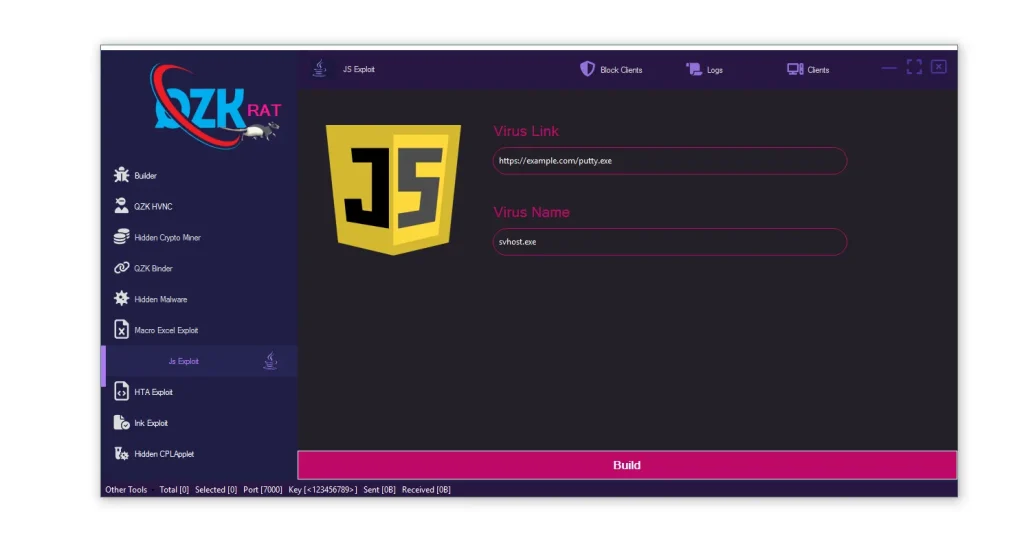
JS Exploit Builder: Generates JavaScript-based malware delivery payloads.

Ink Exploit (LNK Exploit): Uses malicious shortcut files to execute hidden commands.
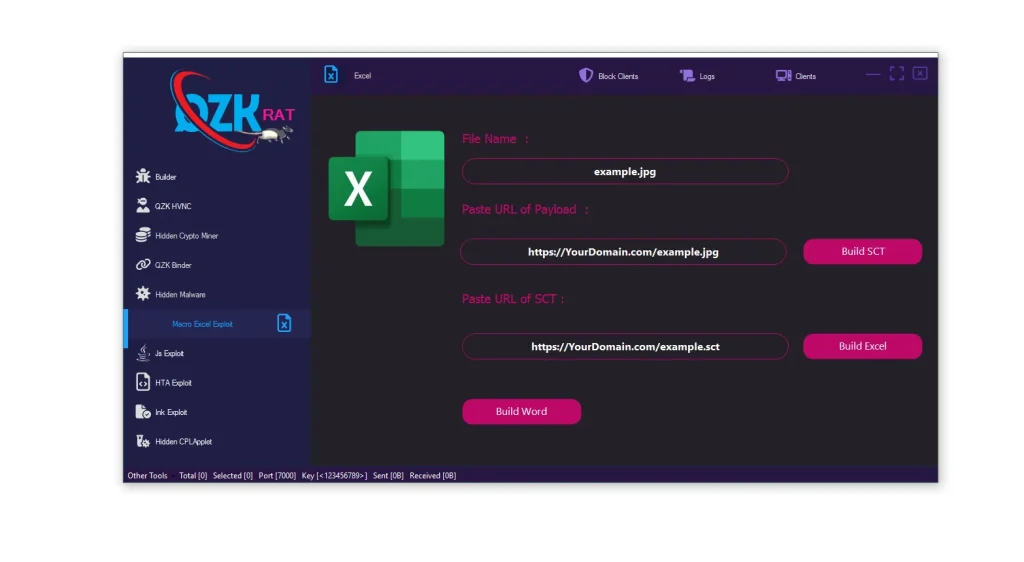
Macro Excel Exploit: Builds weaponized Microsoft Office documents using macro-based delivery.
UAC Bypass: Attempts to gain elevated administrative privileges silently.
Persistence Mechanisms: Maintains long-term access through registry and startup modifications.
USB Spread: Propagates malware through removable storage devices.
Location Tracking: Identifies victim regions and geographic information.
Remote Execute: Executes commands and payloads remotely on infected systems.
File Manager: Uploads, downloads, and deletes files remotely.
Remote Shell Access: Provides command-line control over compromised devices.
Firewall Manipulation: Attempts to weaken or disable Windows security protections.
Behavioral Stealth Features: Uses hidden execution and obfuscation techniques to avoid detection.
Centralized Dashboard: Manages infected clients from a single command-and-control interface.
Hidden RDP / HVNC: Allows invisible remote desktop sessions without user awareness.
Client Tracking System: Organizes infected devices by country, operating system, and status.
Antivirus Evasion: Includes obfuscation and assembly modification features to bypass detection.
https://www.virustotal.com/gui/file/c62b713747d6cff351f1088346caeb4799aa5718bbf073c37f58011e9abc99c7
QZK RAT
MediaFire is a simple to use free service that lets you put all your photos, documents, music, and video in a single place so you can access them anywhere and share them everywhere.
www.mediafire.com